This is the second in a series of posts reporting on the Global Meeting on Gender, Sexuality and the Internet held in Port Dickson, Malaysia from April 13 to 17, 2014, to envision a feminist internet and to evolve a framework for it. Around 50 activists working on gender rights, sexual rights and Internet rights in different parts of the world had come together for the meeting.
In light of the legal, religious, and political contexts in which sexual minorities, activists and people in professions such as pornography and sex work operate, the Internet provides a viable avenue to network, communicate, express, advocate, research, raise funds, etc. This makes them vulnerable to digital threats all the time, the degree and extent of which are defined by several factors. In order to implement security measures, it is worthwhile to examine the nature of these digital threats, the possible consequences of falling prey to them and the appropriate technical responses to them.
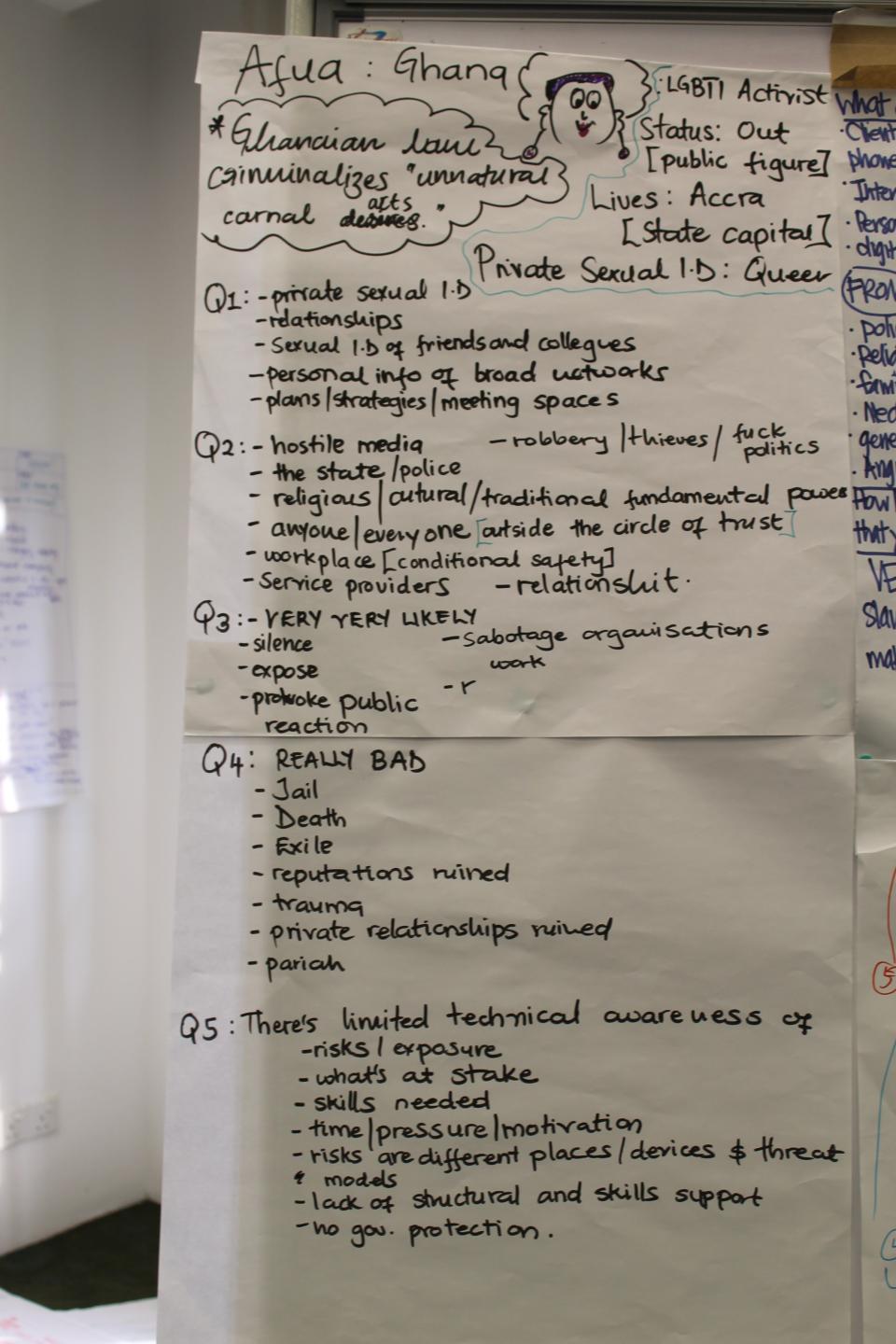
What information and data are at risk?
- In places where homosexuality is illegal, the biggest threat is that of sexual identities being revealed.
- Through the trail of communication and social networking, this could lead to the disclosure of private sexual identities of romantic or sexual partners, families, allies, and colleagues.
- Personal information of intermediaries and people in the extended network
- Organisational activities, plans and strategies, advocacy activities
- Financial information
- Sexting logs, phone call records and other personal communication
Who/ What poses a threat to this data and information?
- Mass surveillance by various governments
- Targeted surveillance towards those who may be under scrutiny for their identities or activities
- The state, police, and law enforcement who may be complicit in state surveillance or may be profiling individuals and groups
- Fundamentalist religious, political and cultural powers that view homosexuality, pornography, sex work etc as unacceptable
- Jilted lovers and crazed exes, who may be in the possession of important information such as passwords or sensitive files
- Crackers (malicious hackers) intending to get access to personal and organisational information, or hijacking accounts, or trying to bring down a website.
- Hostile press that outs identities, intentionally or otherwise and publishes falsified information
What are the potential consequences of not securing information?
- Outing
- Harassment by state, police or other law enforcement, individuals, employers
- Physical or sexual assault, mob justice
- Online and offline abuse
- Extortion
- Take down of content, censorship
- Morphed photos and fake social networking profiles with personal information could be used for impersonation with the intent to defame
- Jail, exile, or death where sexual minorities are punishable with these measures
- Social ostracism
- Loss of employment
- Financial loss or loss of funds caused by the revelation of sensitive financial information
- Loss of reputation and credibility
- Negative impact on personal relationships
- Emotional and psychological cost
- Sabotaging activism; silencing criticism, advocacy and expression
- Hindrances to implementing digital security
- Lack of awareness about the existence of digital threats
- Lack of technical awareness about the potential risks and exposure
- Lack of technical skills to implement digital security measures
- Lack of motivation or time or both to implement such measures
- Absence of structural and skill-based support
- Change in threat models with change in hardware, software and location
- Lack of knowledge about the channels of redress should a breach occur
- In some places, there is lack of legislation protecting citizens from data breaches, online identity fraud and other cybercrimes.
Towards digital security
No security measure is foolproof and new vulnerabilities could occur in existing security tools and mechanisms. Learning about digital security is a continual process. Several groups and organisations work towards digital security education. Cryptoparty is a worldwide grassroots movement aimed at conducting free public workshops for basic digital security. Security In-a-Box is a comprehensive and multilingual resource with several guides, manuals and toolkits for implementing digital security. It also offers reference material and how-to guides according to context, such as Digital security tools and tactics for the LGBT community in the Arabic region.
- 6824 views




Add new comment